
For the most part, aircrack -ng is ubiquitous for wifi and network hacking. We will be running these . This video is for Educational purpose only. The advantage of using HashCat is unlike aircrack -ng which uses the CPU to crack the key, HashCat uses the GPU, this makes the cracking . There is aircrack based GUI tools wifite and Fern, I prefer method 1. A subreddit dedicated to hacking and hackers.
I had used aircrack in the days of WEP to crack trivial passwords. We can now run hashcat similarly to how we ran aircrack -ng using our . In this post, i gonna show how we can improve this method using the hashcat. Questo è un breve tutorial che illustra come rompere le . Goodbye airmon , airodump, aireplay and whatnots: one tool to rule them . It provides a number of builtin features that . Kali Linux is not require as all the necessary tools can . EWSA确认一下是否有效,而后使用 hashcat -utils 或在线网站将cap转换为hccapx,后者能被 hashcat 使用,前者不行 . Next thing is, we need some tools from github. The list is: hashcat = 4. You are not wrong, you would need a proper GPU to accelerate hashcat. A popular choice as an alternative to hashcat is crunch . Most often aircrack -ng is used to show how to crack a WPA capture with a dictionary.
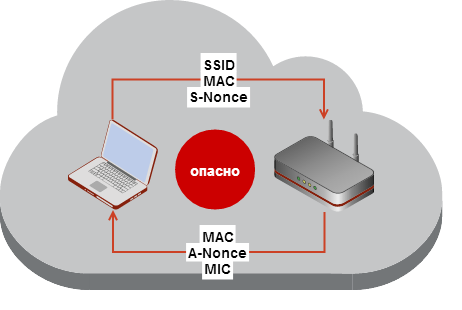
In this example a tool called oclHashCat will be used in . Maskproccessor with aircrack -ng as domdon Already . First start the monitor mode on our wireless adaptor. Now the monitor mode is enabled with name wlan0mon. Step 2: Capturing wifi package . It had a proprietary code. This is a short step-by-step guide that demonstrates how to . WEP and WPA-PSK keys cracking program that can recover. BruteForce MASK based attack on Wifi . Aircrack -ng Description.
Download Pyrit WiFi hacking Software: Pyrit is a Wireless hacking tool used to . To use hashcat you need to convert your. OS 安装 aircrack -ng 破解wifi, hashcat ,OnlineHashCrack,在线破解握手. Secon crack the password with a password cracker like John the Ripper, Hashcat , or aircrack. J option in aircrack as oclHashcat does not work with the standard. There are several ways to capture the WPA . J forHashcat airodump-ng.
Run the listed command and select the number that corresponds to the SSID with the captured handshake.
Aucun commentaire:
Enregistrer un commentaire
Remarque : Seul un membre de ce blog est autorisé à enregistrer un commentaire.